Problem
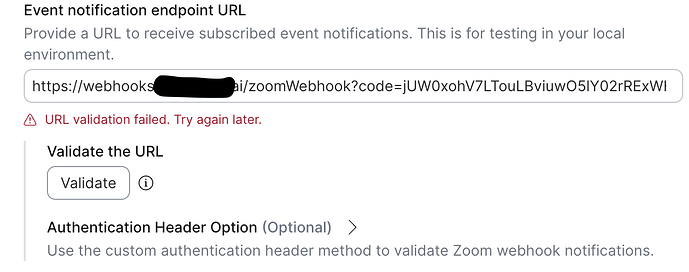
We are ready to submit our application to the Zoom Marketplace for approval but are stuck on an issue with webhook validation.
Our zoom webhook endpoint is a function app hosted on Azure. In the past, we have had no issues with validating it its default Azure domain.
However, after setting up a new domain (one that resolves to the exact same function app, running the exact same code as before), webhook validation fails with URL validation failed. Try again later.
(Note that we set up this new domain because the webhooks endpoint is required to be on the same domain as the rest of our app.)
Summary
 Validation works on old domain: https://therassist-webhooks-prod.azurewebsites.net/api/zoomWebhook
Validation works on old domain: https://therassist-webhooks-prod.azurewebsites.net/api/zoomWebhook Validation fails on new domain: https://webhooks.therassist.ai/zoomWebhook
Validation fails on new domain: https://webhooks.therassist.ai/zoomWebhook- They are running the exact same code and resolve to the same host
- I can confirm that the response looks identical for both endpoints
TLS Certs
The only difference I can think of is the TLS certs. I have confirmed that the TLS cert for the new site is valid: SSL Server Test: webhooks.therassist.ai (Powered by Qualys SSL Labs)
- The cert for the old, working domain is:
- *.azurewebsites.net → Microsoft Azure RSA TLS
- And the cert for the new, failing domain is:
- webhooks.therassist.ai → GeoTrust Global TLS RSA4096
Could it be that Zoom has a list of allowed issuers and GeoTrust Global is not among them? Or, could it be that RSA4096 is not supported?
Debugging We’ve Done
- Confirmed the handler returns
application/json(nottext/plain). - Confirmed both endpoints behave identically with
curl -v(HTTP/2, correct body). - Verified the TLS handshake and certificate chain using
openssl s_client. - Considered whether HTTP/1.1 vs HTTP/2 differences matter (both endpoints support both).
- Looked at DNS — the custom domain resolves correctly to the same IP as the Azure subdomain.
Ask
If anyone has run into this **“**works on default cloud domain but fails on custom domain” situation, especially on Azure App Service, please share how you solved it.
Thanks!